We have been hard at work implementing new changes to make the TLS/SSL certificate management module even more comprehensive and easier to use, integrating input and ideas from our customers. Many new features are now live in our recently released version 10.1.0, now available for download.
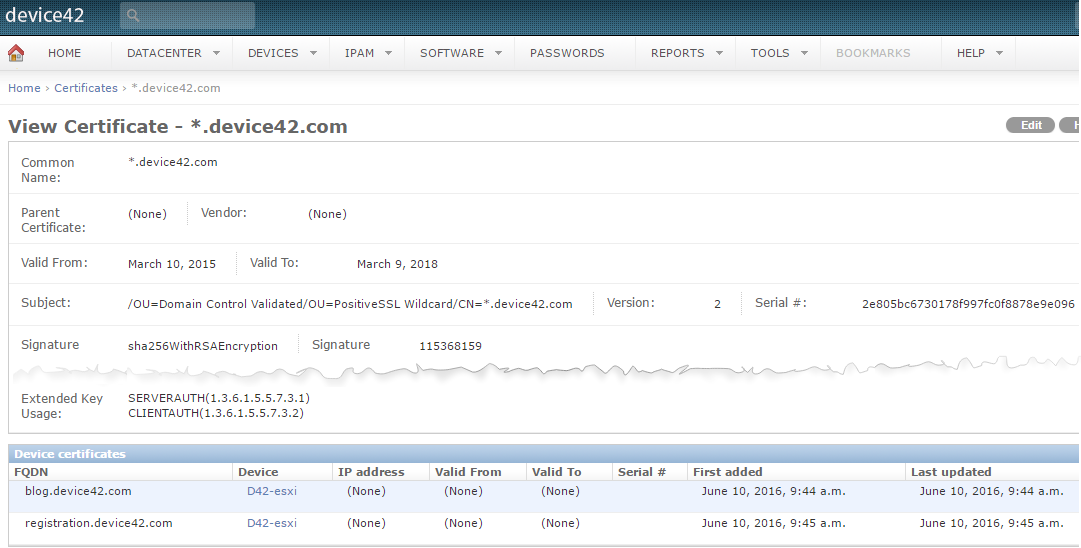
- Associate FQDN, devices, IPs and multiple different validity dates to your certificates
-
For wildcard certificates, you likely have many devices that utilize that same certificate, each with a different FQDN. With this change, you can now easily document this.
[/responsive]
-
When a single device has many IPs and utilizes many different certs – how do you track which certificate belongs to what IP?
-
Conversely, you are likely using the same certificate across many devices. How do you figure out out which devices are still using the older certificate?
[separator headline=”h2″ title=”Auto-discover certificates, device and IP associations.“]
With the newly expanded auto-discovery feature, an IP range can be specified along with port(s) [custom ports supported!] and auto-discovery will walk the entire IP range, automatically importing all discovered certificates, along with all relevant details. These certificates will also be automatically associated with previously discovered devices.
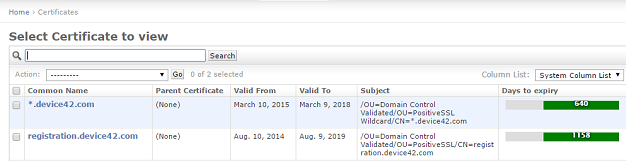
[separator headline=”h2″ title=”Improvements to the list view.“]
List page now includes “days to expiry” as a column, and also features an easy to interpret at-a-glance heat map that visually shows you at a glance how much “life” a certificate has left.
[/responsive]
[separator headline=”h2″ title=”Clarified nomenclature.“]
We’ve also renamed the “issued by” parameter in the certificate details page to “Parent Certificate” to alleviate confusion. For backwards compatibility, issued_by is still supported by the API, but the parent_cert parameter has been added to reflect this change.
[separator headline=”h2″ title=”Reporting enhancements.“]
Though you can have multiple valid-to dates associated with a single certificate, Device42 reports still know to alert you based on the oldest date stored for a given certificate.
This allows you to run reports to see which devices you still need their certificates updated, allowing you to see your update progressing — which can prove especially useful with very large deployments.
[responsive]
[/responsive]