IT Asset Management Reporting: Examples & Best Practices
According to Gartner’s definition, “IT asset management (ITAM) provides an accurate account of technology asset lifecycle costs and risks to maximize the business value of technology strategy, architecture, funding, contractual and sourcing decisions.”
It is not surprising that IT Asset Management (ITAM) reporting is seen as a strategic enabler for achieving IT goals within increasingly agile and modern organizations. Efficient ITAM reporting helps with measuring asset utilization, asset inventory integrity, and return on IT investments.
In this article, we review the use cases for IT asset management reporting in enterprises and explain the purpose of various reports using examples.
IT Asset Management Reporting Framework
As with any other business function, IT asset management reporting requires people, tools, and processes. People, in this context, refers to various roles responsible for managing the IT asset management lifecycle. These roles include asset manager, IT operations and engineering manager, software license manager, IP address manager, SSL certificate manager, data center manager, procurement manager, and business manager. Tools include elaborate spreadsheets and modern ITAM applications designed to manage IT assets, among others. Process binds everything together, creating top-down visibility for management and predictable ITAM outcomes for end-users.
The maturity of an ITAM process is often gauged by the portfolio of reports produced at different stages of an asset’s lifecycle.
- Phase 1: Enterprises deploy tools to discover a comprehensive list of the assets that make up the IT infrastructure.
- Phase 2: The inventory of assets is reconciled across multiple data sources, resulting in a unique categorized list of assets before checking the operational state of each asset for accuracy.
- Phase 3: Assets are used to generate reports that support IT service delivery and Information Technology Infrastructure Library (ITIL) processes like configuration and incident management.
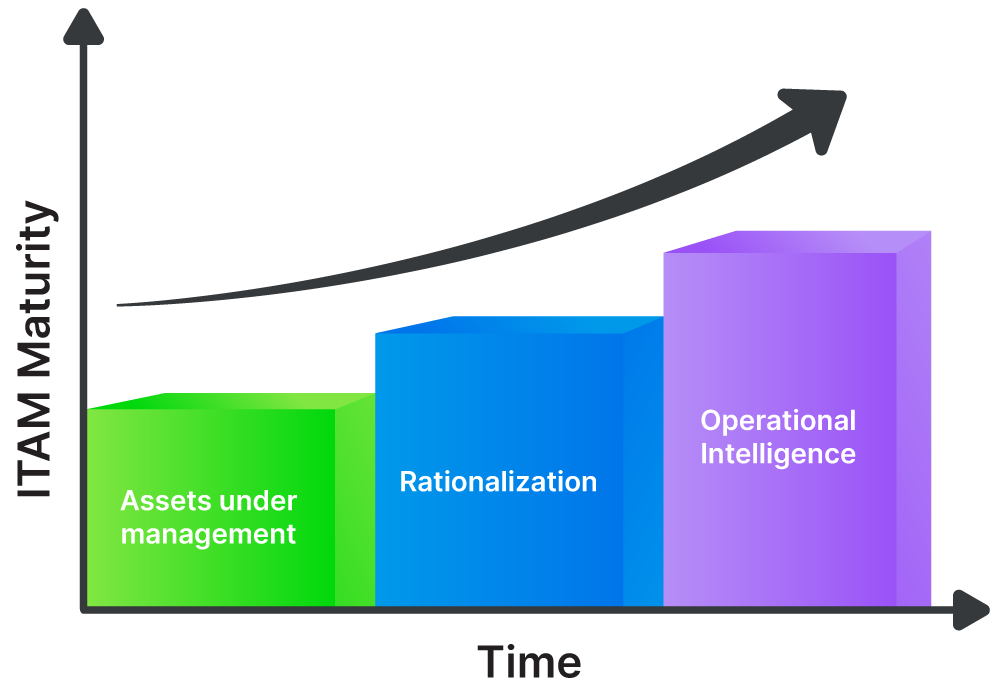
Another way to describe the diagram above is to state that reliable operational insights can only come from a solid foundation created by a comprehensive and accurate inventory of all assets, including hardware, software, and third-party services. The table below provides a summary before we dive into the details and review sample reports.
| ITAM Reporting Focus | Description |
|---|---|
| Assets Under Management | Ensure that all assets are accounted for. |
| Rationalization | Remove redundant asset records and enrich the remaining ones with attributes. |
| Operational Intelligence | Leverage ITAM reporting to drive efficiency and predictable operational outcomes. |
IT Asset Management Report Samples
There are too many ITAM reports and asset management use cases to fit into a single article, so we have selected a cross-section of the reports that we consider to be essential and have included sample screenshots to complement our explanations.
Asset Utilization Report
The asset utilization report lists the assets in use and the total assets available in the organization, which indicates the organization’s overall asset usage efficiency. A large discrepancy between the total number of assets and the number of assets in use may imply a need to move away from a bulk procurement process, for example.
The asset utilization report can also signal a lack of accountability, organizational silos, or a lack of approval workflow processes. It’s particularly important for defining reclamation rules for your software assets.
This analysis should consider the operational status of an asset, such as being inactive or in maintenance. This status can be used for filtering to determine the cumulative computing power available to an application, department, or data center at any point in time.
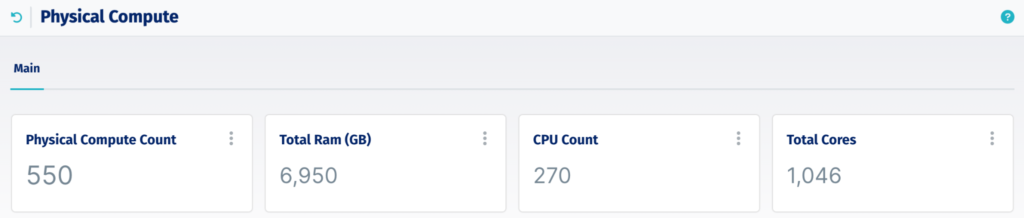
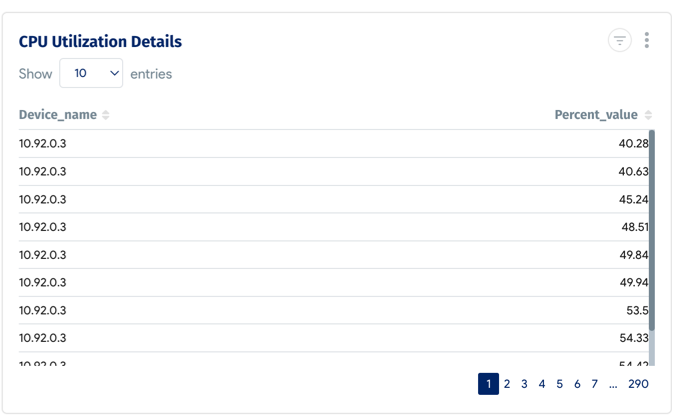
Keep in mind that an asset may show as being operational while not hosting any workloads. Monitoring the aggregated utilization rate of assets resources such as CPU and memory helps validate the operational status of the assets. It’s also best practice to group this report by manufacturer to identify the vendors that provide the least used assets, a perspective that can help procurement managers.
The agentless monitoring of devices starts by discovering their IP addresses before collecting time-series data of their resource utilization and aggregating the values over a period of time such as a day or a month.
Asset Expansion Report
Comparing the new assets purchased in an environment to the number of existing assets can help with demand forecasting and detecting unexpected jumps in purchasing behavior within a distributed IT organization. This report requires integration with the enterprise procurement applications used by finance departments to track purchase orders. It’s also necessary to complement the procurement data with asset attributes collected from tools used to discover systems on the networks.
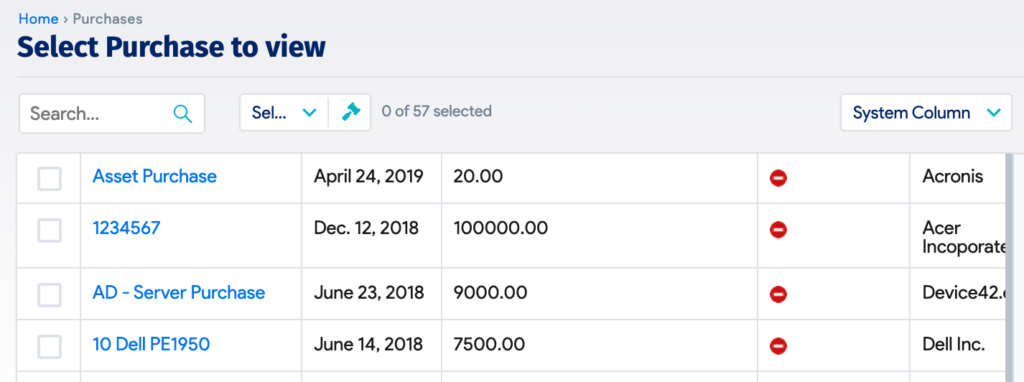
Comparing the records from the procurement systems (sample screenshot above) with the systems added to the enterprise network (sample screenshot below) is a helpful way to cross-check that the purchased systems are being deployed as expected.

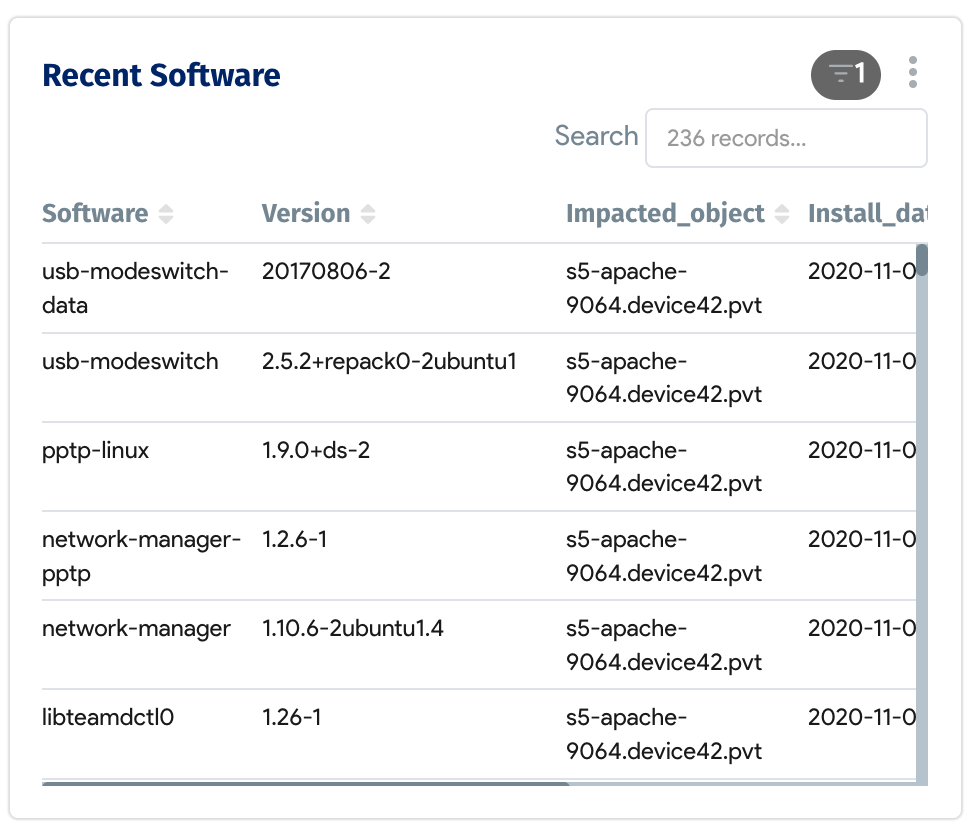
Software License Usage Report
Large enterprises often license various productivity, computing, and ERP software tools for overlapping purposes or to solve the same problem. Knowing the utilization by software vendors helps procurement managers prepare for annual license renewal plan and negotiations. Under utilized licenses can help drive down cost, while, overused licenses can lead to hefty penalties which can be avoided.
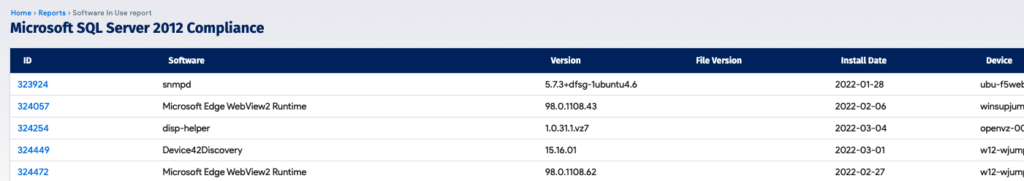
This report can help business units monitor their costs and usage, define coordinated reclamation policies, and drive the procurement department’s priorities.
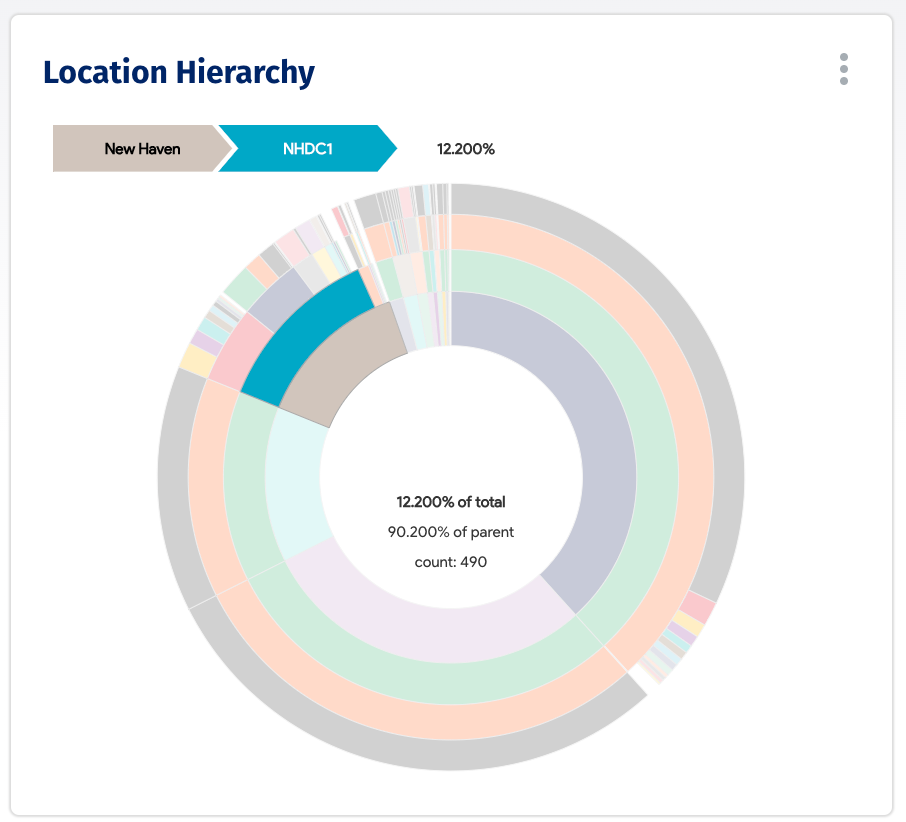
Assets by Location Report
The knowledge of where the company’s assets are physically located helps inform decisions about where to open new data centers or store spare parts. It can even assist with filing state-specific tax reports that require asset depreciation values included in the financial statements.
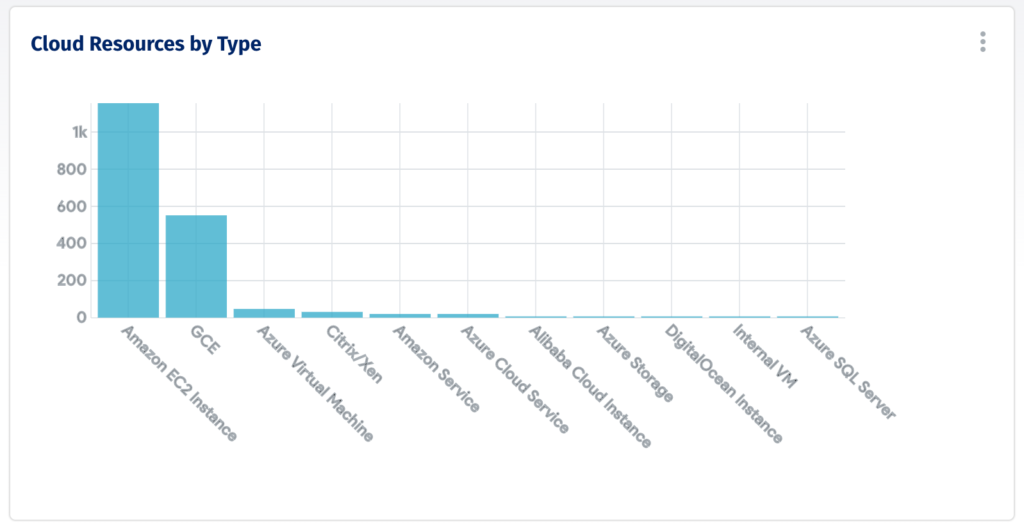
Assets by Cloud Provider Report
As assets migrate to the cloud, it helps to know which provider is hosting the company’s assets to help:
- Know where you have leverage to negotiate better pricing contracts based on volume and usage
- Know if you have any a single points of failures based on region where the assets are located
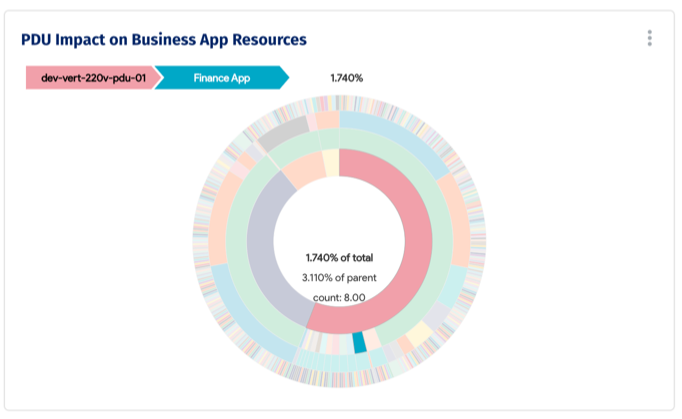
Assets by Power Distribution Unit Report
It’s important for organizations operating data centers as part of a hybrid cloud strategy to keep an eye on the power distribution units (PDUs) that deliver power to hardware devices. To avoid creating a single point of failure, it’s a best practice to not overly depend on a single PDU. This report helps identify at a glance when it’s time to deploy a new PDU in a data center.
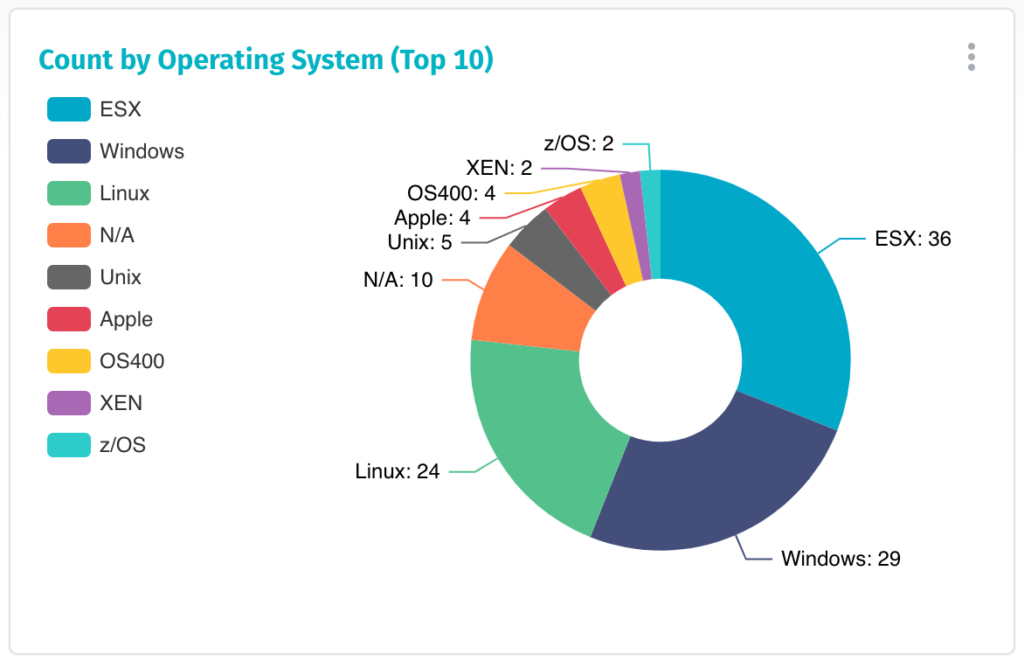
Assets by Category Report
Decision-makers and sponsors in the organization are always interested in understanding the various categories of assets to better control capital expenditures. This exercise begins by understanding how many software licenses, printers, desktops, and storage devices are in use.

Using operating system types as an example, the Assets by Category Report sheds light on which OS application developers prefer to use and which outdated and unsupported versions may still be running in the company and should be replaced.
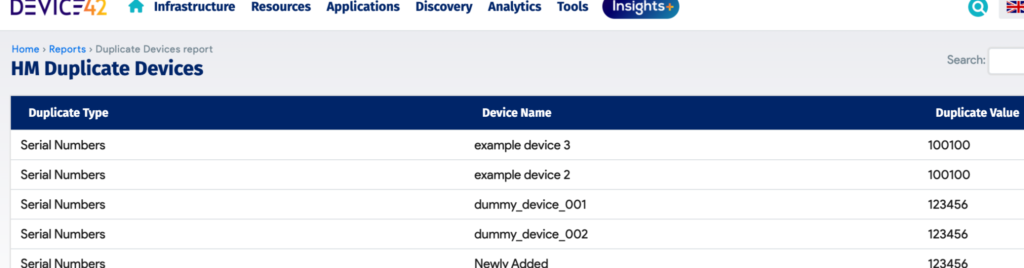
Duplicate Assets Report
Duplicate records are the most common cause of confusion in asset inventory databases because enterprises leverage multiple discovery tools to ensure that all assets are identified and to collect complementary asset attributes from various sources, which results in duplication. Pivoting on unique identifiers to deduplicate assets is a normal part of the asset management process and is required to build trust in the inventory database before it can be widely adopted for operational reporting.
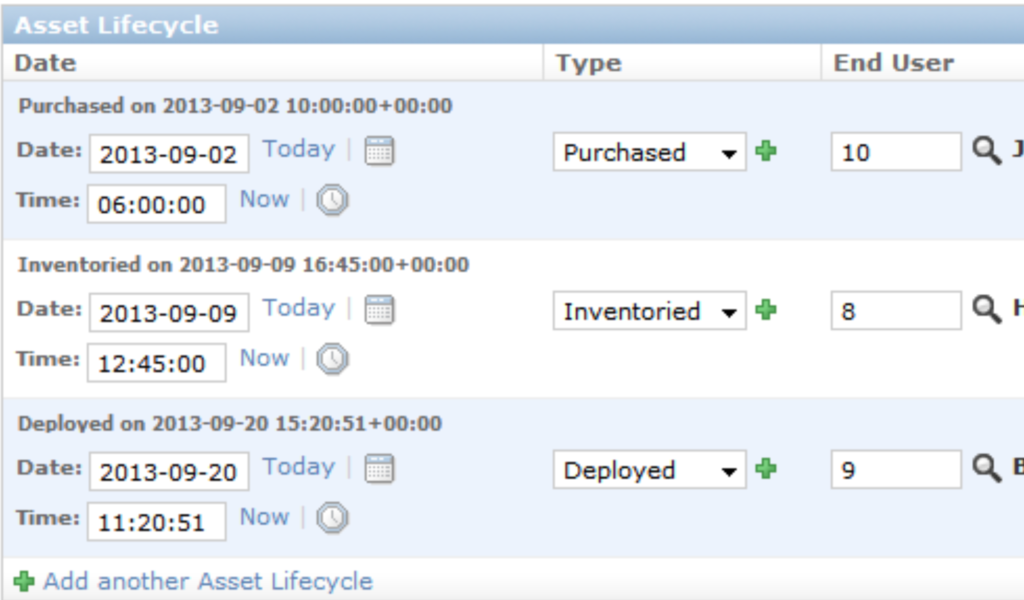
Lifecycle Management Report
Keeping track of where assets are in the lifecycle helps with regulatory compliance, financial reporting, and IT service management. Each company may define the lifecycle of its assets slightly differently, but the ITAM lifecycle generally includes stages such as planning, procurement, deployment, integration, maintenance, upgrade, and disposal. It helps to use an asset management tool that allows customization of the stages that define the lifecycle based on asset categories.
IT Service Management Operations Report
One of the main use cases of IT asset management reporting is increasing visibility into IT service management (ITSM) processes such as incident management, change management, problem management, and service request management.
For example, the incident and configuration management processes rely on this report to stop managing devices as they reach end of life and to install agents on new servers that come online.
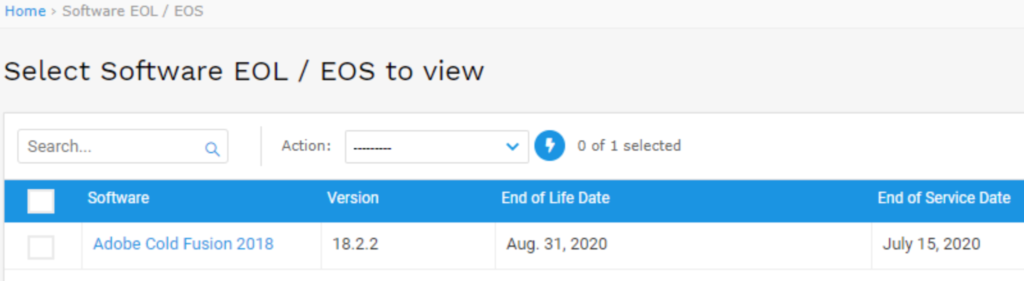
Hardware End-of-Life (EOL) Report
If you need a more granular view of the hardware lifecycle, the end-of-life (EOL) report can be quite useful. This report can point to assets that should be retired based on company guidelines and could send notifications to plan the necessary engineering steps involved in shutting down and replacing equipment housed in data centers. Not all assets are part of the infrastructure, so the asset management report should include middleware assets such as databases as well as software applications.
Benefits of IT Asset Management Reporting
There is a spectrum of benefits derived from ITAM reporting, including the following.
Transparency for All Stakeholders
A basic function of ITAM reporting is to drive visibility and consistency across the views provided to different stakeholders, including procurement managers and IT operations engineers. This unified perspective helps avoid inefficiencies and prevent mistakes.
Support for Improvement Initiatives
ITAM reports track quantitative measurements such as demand, usage, and performance, which helps guide and prioritize improvement initiatives.
Audit and Compliance
Public and private organizations in many areas, such as healthcare, financial services, and the federal government, are subject to government regulations and cybersecurity audits that can’t be enforced without the help of IT asset management reports. For example, compliance depends on audit trails that track configuration changes made to IT assets and send warnings if unauthorized changes are made. Such enforcement depends on an accurate and current list of assets with a complete set of attributes.
Efficiency and Return on Investment
ITAM reports track the costs and capacity utilization of assets, grouping them by application, department, and business unit, which helps financial managers identify and bring attention to wasted resources.
Common ITAM Reporting Pitfalls
The Need for Administration
ITAM reporting may generate a large volume of reports over time that lack a clear purpose, created by users who may have left the company or transferred to another role. An administrator with subject matter expertise and a cross-departmental mandate must regularly match reports with active use cases, communicate with the owners of the reports, and archive unused or duplicate reports.
Inadequate Technology
It’s not uncommon to find outdated and partial lists of assets tracked in multiple versions of spreadsheets throughout an organization. It’s also common to lack the technology required to map IT assets to applications and business processes, which makes it nearly impossible to use the data for compliance and IT service management purposes.
It’s necessary to leverage modern tools equipped with dynamic asset discovery technologies, deduplication algorithms, and dependency mapping capabilities. An IT asset management initiative without a current and accurate list of assets and dependencies can be more damaging than helpful.
Conclusion
An IT asset management reporting solution evolves through three stages of maturity: asset discovery, which delivers a comprehensive list of assets; rationalization, which is required to deduplicate and enrich the asset records with attributes to create a unique and accurate list of assets; and finally operational intelligence, where trusted reports support IT service management activities such as incident and configuration management. The implementation of an IT asset management solution rests on a platform that can deliver automated discovery, trustworthy reconciliation, and integrated reporting.