FEATURES TOUR
Enterprise Password Management
Device42’s enterprise IT password management software centrally and securely manages shared passwords used between IT teams.
- Auto-generate secure passwords
- Automatic logout on inactivity
- Easy search features
- Securely Copy passwords to clipboard without displaying them
- Optionally assign password to multiple devices
- AES 256 bit encryption for both storage and backup
- Permission control per password
- Optionally store as non-retreivable ‘Burnt Secrets’ or externally with CyberArk integration
- Password are not in HTML views and are only retrieved when requested

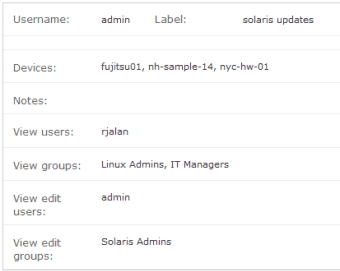
Granular Permission Control
Device42’s network password manager controls who can view and change passwords at the global or per-password level:
- Users who can view the password
- Groups who can view the password
- Users who can view and edit the password
- Groups who can view and edit the password
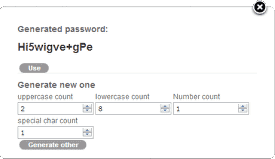
Secure IT Password Generator
Device42’s password generator creates auto-generated long, strong, and unique passwords that provide optimal password security.
- Generate strong, random passwords
- Custom security settings for generating passwords (Quantity of uppercase, lowercase, special, and digit characters)
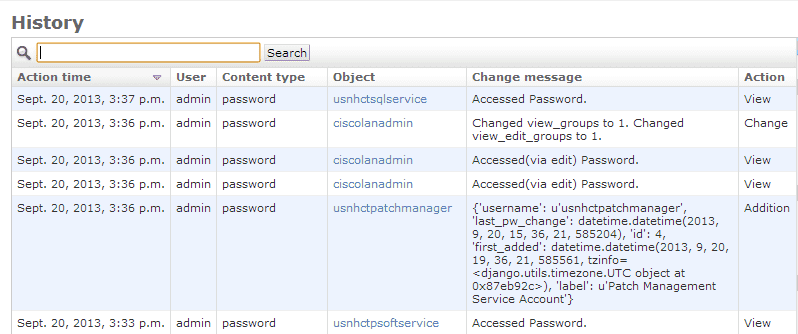
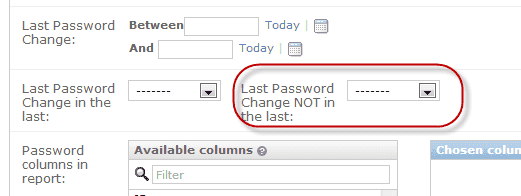
Password History and Audit Trail
Device42 password and history audit trails ensure that every password change is recorded and tracked ensuring full visibility and fail-safe password tracking.
- Device42 logs all actions, providing a built-in, searchable audit trail
- Password related actions are logged: adds, changes, deletes, and even password viewing is logged
- History is easily accessible via the centralized reports menu, or via the history button found on each password page
- All prior passwords are retained in an encrypted fashion
Run IT with confidence.®