A Free Guide to Cloud Migration Security
While planning a migration to the cloud, organizations must not be too hasty to focus only on the potential benefits and end up forgetting to address critical security concerns. Gartner predicts that 45% of IT infrastructure and software spending will shift from traditional solutions to the cloud by 2024. The interest in public cloud hosting and services has mainly been driven by digital transformation initiatives intended to quickly leverage innovation at scale and take advantage of new capabilities such as AI/ML, in spite of budgetary constraints.
Even though public cloud service providers (CSPs) have the muscle to provide state-of-the-art security controls, enterprises must be very clear about what their security requirements are before moving to the cloud and to understand what their responsibilities are in configuring said controls. Migration to the cloud exposes organizations to cybersecurity threats of accidental or malicious data exposure, corruption, or loss. These may arise from exploited vulnerabilities such as poor configurations, unsecured data transfer mechanisms, or improper assignment of permissions. According to the Check Point 2022 Cloud Security Report, misconfigurations were the top security-related incidents, accounting for 23% of all incidents.
To ensure that organizations are better prepared to migrate securely to the cloud, we have outlined several best practices and associated concepts related to this topic. The focus of this article will be on cloud security pertaining to migration to the CSP’s own infrastructure (i.e., IaaS, PaaS, and SaaS offerings), so collocation will be excluded.
Summary of cloud migration security key concepts and best practices
The table below describes three essential cloud migration security concepts that will be addressed in the following discussions of cloud migration security best practices.
| Security concept | Description |
|---|---|
| Shared responsibility | Establishing the security boundary between the CSP and the client |
| Cloud IAM | Visibility and control over the assignment of permissions and resources to users |
| API security | Implementing controls at API endpoints to mitigate vulnerabilities |
The table below describes the most important cloud migration security best practices, which we cover in detail in this article.
| Security best practice | Description |
|---|---|
| Conduct pre-migration risk assessment | Assess, evaluate, and treat migration-related risks to data, applications, platforms, and users. |
| Align to CSP security recommendations | Understand and adopt CSP guidance related to the architecture, design, and deployment of cloud-native solutions. |
| Update identity and access management (IAM) controls | Map on-premises user permissions to cloud-centric roles. |
| Implement end-to-end security monitoring mechanisms | Monitor across the stack, including integrations and user behavior. |
| Ensure compliance with sector-specific security regulations | Identify and comply with applicable regulations such as GDPR and HIPAA. |
Conduct a pre-migration risk assessment
The migration from an on-premises environment to a CSP environment invariably introduces risks from a security perspective. Failing to identify, assess, and mitigate security-related risks can hinder realizing the full value of moving to the cloud. Organizations must be cognizant of their risk appetites when planning this migration and analyze all the aspects that require controls in order to mitigate impact.
A formal pre-migration risk assessment approach using a framework such as ISO 27005 would usually involve reviewing information and holding conversations with various stakeholders involved in the technology, legal, and human capital domains and then collating the information in a risk register. Deployment of technology solutions to analyze the on-premises environment and identify migration-related risks would greatly enhance this process by providing more in-depth knowledge of the current state of the organization’s infrastructure and systems. Solutions from Device42 or Appscore would be very useful in providing such capabilities.
Areas that an enterprise must focus on during this pre-migration risk assessment include the following.
Managing risks related to specific workloads
Organizations need to evaluate the criticality of workloads and the associated risks related to them. For example, applications that process data associated with customer information or business transactions would be deemed more valuable than those related to internal business activities.
Securing data both at rest and in transit is critical, as is managing access to said data, especially where legal or regulatory ramifications may apply. Adopting guidelines (such as the ISO/IEC 27018:2019 standard) on securing sensitive data like personal identifiable information (PII) in the public cloud is recommended.
Managing risks related to performance (availability and capacity)
The reliability of the cloud environment being migrated to is also a focus area for the assessment of security-related risks. During planning, a review of the history of outages experienced by CSPs would be a good source of reliability information. In addition, the review of terms and conditions related to redundancy, service continuity, and credits would also be useful information to feed into the risk assessment. Ultimately, no cloud environment is perfectly safe, so testing dependencies and preparing contingency plans during migration will be necessary mitigations to consider.
Managing risks related to users, including knowledge gaps
Migrating to the cloud might be challenging for IT staff who have been dealing with on-premises systems. Without the necessary upskilling and support, the chances of security risks materializing are high since the staff may end up failing to apply the right security controls.
A rigorous skills assessment followed by the implementation of a training program can help mitigate this risk. Bringing on board skilled partners to handhold the IT staff during the migration can also help. A formal organizational change management (OCM) program needs to be instituted alongside the training to address fears related to job security and satisfaction.
Align to CSP security recommendations
When it comes to cloud migration, the security posture is a shared one rather than outsourced, with each party having its own distinct responsibilities. It’s like renting an Airbnb: The host has invested in security mechanisms, but it’s up to you to keep the door locked and not provide access to untrusted parties.
The concept of shared security is one that CSPs communicate up front as they onboard you into their environments. As AWS puts succinctly, the provider is responsible for the security of the cloud, i.e., the underlying infrastructure (servers, networks, and physical environment), while the customer is responsible for the security in the cloud (data, configurations, and identity and access management).
According to ITIL 4 guidance, any organization migrating to the cloud should understand the level of security as provided by the CSP, including guidance, attestations, and audit reports. In addition, the organization should define how it will secure its use of cloud services and use the security-related features provided by the CSP. Areas of responsibility depend on factors such as the type of service relationship, service packages to be procured, customization levels, necessary integration, and applicable laws and regulations.
While an enterprise might be tempted to mirror its on-premises configurations within the cloud environment (lift and shift), transferring the existing security configurations might not be appropriate for the cloud, resulting in the introduction of vulnerabilities. A better approach is adopting the CSP’s security guidance, which has evolved over time to identify the best controls for a given set of cloud services.
CSPs have the capacity and resources to research and deploy best-in-class security, so their recommendations on security architecture design and deployment practices are worth their weight in gold. Adopting the CSP security guidance involves considering a variety of aspects, including identity and access management (IAM), data security, network security, and threat protection. Borrowing from the expertise of CSPs, with guidance such as the Well-Architected Framework, can ensure that an organization’s cloud migration journey is benchmarked to the most optimal set of security controls.
Once an appropriate security architecture framework is adopted, the next logical step is enabling these cloud-security-recommended controls. These vary depending on the services to be acquired from the CSP and internal governance requirements such as workload criticality and data classification. Such controls include industry-standard encryption at rest and in transit, implementation of least privilege access, configuration of firewalls, automation via DevOps to limit human error, and adoption of security monitoring tools, among many others.
For example, while Azure will automatically encrypt your data at the service level using 256-bit AES encryption, you can implement a second layer of encryption at the infrastructure level to mitigate the loss of encryption keys. For firewalls, it is recommended to block all traffic by default and only allow specific traffic, protocols, and ports on individual instances. Regular auditing of the implemented controls is recommended and is better carried out by independent third-party specialists.
Update identity and access management (IAM) controls
One of the significant risks in cloud migration security emanates from abuse or mishandling of credentials. Migration creates opportunities for credential theft, especially for those with administrative or super-user privileges. In addition, insiders may use their new credentials in the cloud environment to perform actions or access data items that are unethical or contrary to their expected responsibilities.
A best practice is to create or update existing IAM controls in line with the guidance provided by the CSP. The concept of Cloud IAM as defined by Gartner is the security and business discipline that includes multiple technologies and business processes to help the right people or machines access the right cloud assets at the right time for the right reasons while keeping unauthorized access and fraud at bay.
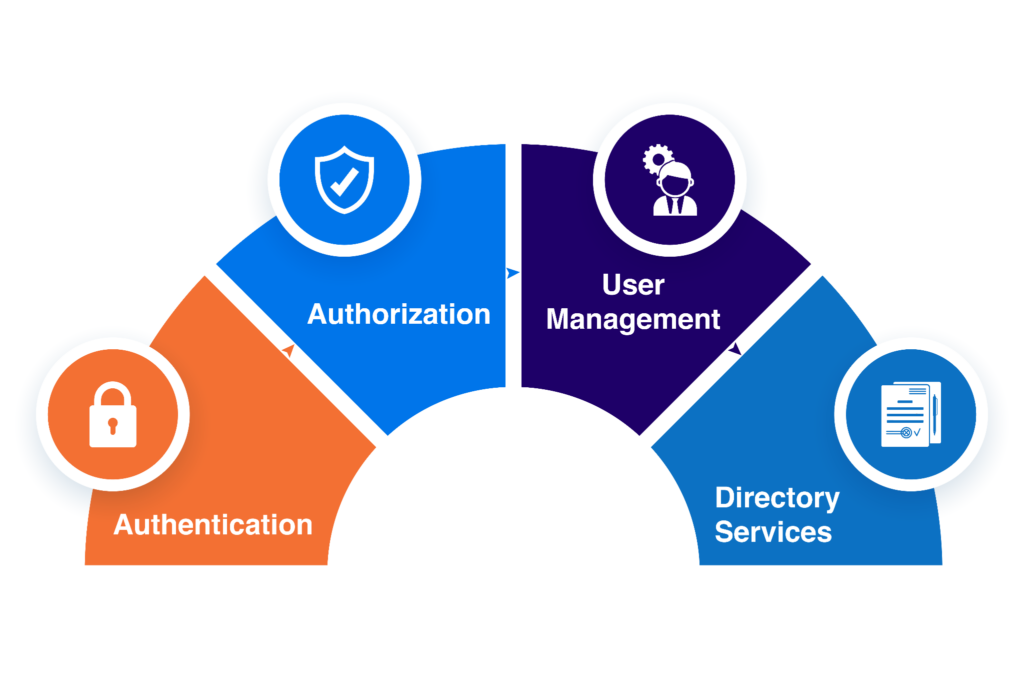
Cloud IAM components
Cloud IAM is broad since it is not just human users that access cloud systems—both internal and external systems do as well, and their access must be carefully managed. That means categorizing identities, assigning them the relevant rights, and regularly monitoring and auditing access levels. This can be a significant challenge when migration involves thousands of users, microservices, integrations, and tools, thus meaning the handling of many secrets, keys, and certificates. Keeping tabs on all these dependencies is a huge headache for any organization migrating to the cloud.
Some important actions to mitigate cloud migration security risks related to IAM include updating and testing existing IAM policies as part of the cloud migration process. Mapping of on-premises roles to cloud-centric roles is a critical activity during migration planning because this ensures that all users and permissions are accounted for prior to assignment within the cloud environment. In addition, adopting a role-based access control approach ensures that only authorized staff are allowed to provide and maintain cloud resources.
Deployment of CSP-recommended IAM tools for configuring and monitoring accesses and privileges is another consideration when it comes to cloud migration security. Techniques such as zero trust have come to the fore, where no entity (internal or external) is automatically trusted or granted access to any cloud resource without prior verification (authentication, authorization, and validation) at each instant. Organizations can also leverage managed security services and the expertise provided by CSPs or renowned partners to help manage cloud IAM and deploy related tools.
Implement end-to-end security monitoring mechanisms
Organizations that have become accustomed to on-premises environments find it a challenge to account for their assets and resources once migration to the cloud is underway. Infrastructure and workload visibility is an integral part of security, especially where the required resources and data span a complex hybrid or multi-cloud environment. During migration, monitoring is necessary to check potential issues related to security and performance in the cloud. Once migration is complete, monitoring must continue to check that workloads and controls function as expected, CSP SLAs are on target, and resource consumption matches the forecast.
It is critical that organizations invest in the right tools that ensure end-to-end visibility of all cloud assets and resources, including APIs. APIs are the primary communication mechanisms among services in the cloud, so monitoring this transfer of data across resources and architectures is critical since it is a potential source of security vulnerabilities such as unwarranted data exposure or poorly configured authentication mechanisms.
The concept of API security during cloud migration involves implementing controls at API endpoints to mitigate vulnerabilities. This starts with understanding the data’s source, destination, and route, then defining the security requirements at each and applying the CSP’s recommended tools for monitoring and controlling data transfer and storage. Tools like Apigee Sense identify patterns that might represent suspicious API requests and take action to flag or block them.
End-to-end monitoring should not just focus on resources but also monitor unexpected changes in configuration and user behavior. While this is relevant for any environment, cloud migrations are notoriously prone to exploitation by actors who would want to make malicious changes to systems. As such, monitoring unauthorized changes—such as modification of resources or escalation of privileges—has to be carried out during and after migrations. Establishing a baseline based on the chosen architecture and design is a critical step that will support the monitoring of configurations and user behavior.
CSPs have a variety of monitoring tools at their disposal, most of which can automate what is routinely conducted manually in an on-premises environment. For example, AWS CloudWatch will both provide observability capability and continuously analyze logs and metrics.
Organizations should seek to automate all possible actions that involve detecting, responding to, and resolving security incidents during cloud migration. Two key areas that can benefit heavily from automation are log analysis and incident response. The number of logs generated during migration can overwhelm a team used to on-premises environments, so it makes sense to adopt tools that can leverage machine learning capabilities on the cloud to correlate logs in order to rapidly detect security intrusions or unearth vulnerabilities. Security incident response can also be automated based on agreed rules, including swift isolation of infected resources or restriction of rights where patterns that go against policies are detected.
Ensure compliance with sector-specific security regulations
From a security standpoint, identifying and complying with applicable legislation, regulations, and standards that could impact your organization’s cloud migration are critical undertakings. Failure to comply could expose your enterprise to penalties, operating license withdrawal, or lost customer confidence. Selecting the right CSP is an important decision that should be evaluated not just from the technical and financial perspectives but also based on whether they can support your organization in meeting compliance requirements such as those related to data privacy, location, or processing.
CSPs will openly provide communiques from audit bodies showing that they comply with requirements, but they generally do not allow customers to conduct audits themselves. An organization seeking to migrate may end up relying on third-party audits and attestations as evidence that the selected CSP provides compliant environments.
Examples of such compliance regulations include:
- GDPR: This EU-centric regulation is the gold standard for data privacy. Organizations migrating to the cloud and handling personal data belonging to European citizens will need to select a CSP as a processor that complies with the requirements of securely processing personal data within European borders.
- HIPAA: This US law ensures that organizations use and disclose an individual’s health information properly and safeguard it appropriately. Organizations that handle US citizen health data and are migrating to the cloud will need to select a CSP that can show that its cloud environments are securely designed to protect such data.
- PCI-DSS: This standard covers the handling of payment card industry data. Organizations involved in merchant card transactions need to select a CSP whose cloud environment is secured by implementing security controls that meet the prescribed PCI standard requirements.
It is important to note that compliance cannot be outsourced, so organizations migrating to the cloud still need to play their roles in selecting the right CSP, tracking compliance status, and implementing the controls that are within their scope of shared responsibility, such as encryption, network controls, and IAM.
Recommendations
Understanding the state of your IT assets and security requirements is the first step of security in cloud migration. Lack of visibility before and after migration is a significant security lapse that can be exploited to cause much harm. During planning for migration, organizations should undertake a comprehensive risk assessment exercise to ensure better preparedness in dealing with security issues during migration. Leveraging guidance from CSPs regarding security configuration is the shortcut to a better security posture in all dimensions, including access management and compliance, but keep in mind the shared responsibility model.
Conclusion
This article provides guidance to any organization whose digital transformation strategy includes the need to migrate its infrastructure and systems to the public cloud. It is imperative for enterprises to implement the aforementioned cloud migration security best practices to protect their systems and data, achieve their goals, and satisfy the expectations of their stakeholders and consumers.
Any organization that does not account for security in cloud migration will most likely fail to achieve full value since confidentiality, integrity, and availability are the hallmarks of valuable business data. It is obvious that a poorly planned migration is a security vulnerability in itself, so security must be incorporated in all phases of the cloud migration exercise, from planning through deployment. Adopting best practices in cloud migration security provides assurance that an enterprise is committed to securely extracting value from the move to the cloud.




