We have updated the Device42 python discovery script [ download v1.2.0! ] that grabs system inventory information from linux machines using a specified range of IP addresses. Dependencies and usage tips are discussed below.
Updates
- Now detects attempts to discover non-unix machines
- Ensures supplied credentials logged onto the machine
- Can now define custom SSH Port
- Various minor bug fixes
Dependencies
We have tested this script with python 2.7.x.
The script depends on paramiko library(released under LGPL license, enclosed with the repository).
There are multiple ways you can install paramiko.
If you have pip setup on your system, you can just do:
sudo pip install paramiko
Otherwise, You can download the package from Paramiko Pypi page
and install it with
sudo python setup.py install
On ubuntu/debian based system, you can also do:
sudo apt-get install python-paramiko
Required changes in the script
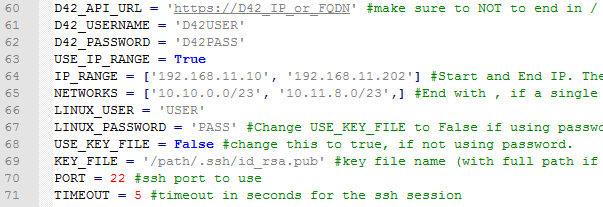
[/responsive]
Before you run the script, you need to add device42 IP/FQDN credentials, IP range and Linux user credentials info as shown above. Lines 30-37.
Most of these are self-explanatory, but lets talk about password vs. key file for a minute.
LINUX_PASSWORD = ‘PASS’ #Change USE_KEY_FILE to False if using password. password for linux servers. not required if using key file.
USE_KEY_FILE = True #change this to true, if not using password. KEY_FILE = '/path/.ssh/id_rsa.pub' #key file name (with full path if not in same directory as the script)
If you want to use the password for linux machines on the network, you have to set USE_KEY_FILE = False.
To use the key file, you have set USE_KEY_FILE = True and add the full path of the KEY FILE as KEY_FILE.
Optional changes in the script.
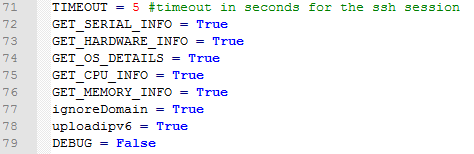
[/responsive]
LINES 38-46 are optional settings for the script.
For example, with GET_OS_DETAILS = False, you can turn off the OS detail gathering in the script.
ignoreDomain = True, ignores the domain suffix found in name.
Running the script
[/responsive]
You can make the script executable:
$ chmod +x <script.py>
or run via:
$ python <script_name.py>
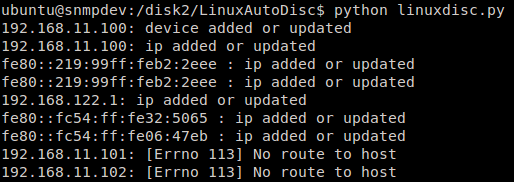
With flag ‘ DEBUG=False ‘, the script will list each IP including the result of success/failure. Success or failure message for uploading an IP for that machine are also displayed.
Getting the script
The script is available via Github @ Device42 AutoDiscovery Scripts Repository – under ‘src’ folder, grab the file ” linux_auto_dics_multi.py “.