5 Minute NIS2 Checklist: Assess Your Cyber Resilience Today
NIS2 is a European Directive published in 2022 that provides a framework for harmonizing organizational approaches to cybersecurity management. NIS2 demands taking appropriate operational, technological, and governance measures to protect a company’s environment and its assets. While applicable in the European Union, NIS2 represents a significant regulatory advancement and a valuable reference for implementing cybersecurity best practices globally.
NIS2 is enforced for organizations operating in critical fields, such as energy, healthcare, financial services, public administration, and other key infrastructure sectors. However, certain compliance obligations from NIS2 also apply to other industries, including postal services, manufacturing, and food retailers.
To help you better understand the NIS2 requirements, their objectives, and practical implementation, this article provides a comprehensive NIS2 checklist for any organization to follow, regardless of its field or jurisdiction.
Key NIS2 checklist requirements
| Requirement | Description |
|---|---|
| Risk management and information security governance | Start with appropriate management support for developing an information security program. |
| Asset management | Discover, manage, protect, and monitor assets throughout their lifecycles through appropriate tools and ownership. |
| Supply chain security | Manage a third-party due diligence process, ensuring that all new systems are identified and assessed adequately before connecting to your environment. |
| Network and application security | Deploy technical controls such as network segmentation, encryption in transit, intrusion detection systems, and log collection and analysis. |
| Identity and access management | Manage identities, recertify accesses, and implement strong authentication for critical systems. |
| Incident management | Implement a solid response plan with scenario playbooks and incident response training. |
| Business continuity and crisis management | Prioritize your critical processes and create strategies for recovery in the event of crisis situations. |
| Training and awareness | Continuously train staff on information security risks and appropriate actions in order to report suspicious activity. |
Risk management and information security governance
Any successful internal program, including information security, starts with proper governance. Whether it’s a startup or a large enterprise, leadership needs to support the development of a strong cybersecurity program by providing resources, endorsement, and open communication. While decision-makers do not always see security and risk management as a priority, leveraging regulatory requirements can be an effective way to secure management support.
Noncompliance with the NIS2 Directive for companies in scope—or with other applicable regulations, such as DORA and GDPR in the EU, or HIPAA, FISMA, and GLBA in the US—is simply not an option. The consequences of ignoring regulatory requirements can be fines, regulatory scrutiny, audits, and even a bad compliance reputation. While implementing minimum compliance is seldom enough to properly secure organizational assets, it’s a necessary starting point.
Requirements may be addressed proportionally. For instance, in a startup, a simple risk management process may be in order, such as conducting an annual risk assessment and regularly tracking and mitigating the most important concerns. Mitigation is usually achieved by implementing security controls, which may be done internally or outsourced. If access management is a high risk, for example—and it usually is—any critical SaaS purchase should require an SSO integration to minimize the chances of unauthorized access.
In large companies, extended risk management and security teams are required to identify risks and continuously secure assets. Strong policies and procedures, supporting tools, and risk reporting processes need to be implemented, with frequent risk assessments, security posture monitoring, and improvement.
Asset management
An asset is anything of value, and in the context of cybersecurity and the NIS2 checklist, it refers to any system or device that processes data, whether it’s a database, SaaS application, IoT, configuration item, or endpoint.
The first step in protecting assets is to identify them. In this day and age, this is not easily managed without a dedicated software solution that continuously identifies and maps assets within the company’s environment. To ensure full compliance, visibility, and a secure baseline, the asset inventory must run automatically.
Solutions like Device42 address this challenge through a wide array of features, including cloud and infrastructure asset discovery, upstream and downstream dependency mapping, lifecycle tracking, ownership enablement, insights and reporting, and more. Service management, software lifecycle management, and IT and security operations need to leverage a centralized asset management system that integrates with necessary data sources to effectively manage asset security.
NIS2, like other frameworks, emphasizes asset management for a simple yet key reason: You can’t protect assets you are unaware of. With constant system changes, new vendor onboarding, sudden enablement of AI features in applications, and new devices connecting to the environment, new vulnerabilities are likely to appear. For this reason, centralized asset management has become a crucial security control in its own right.
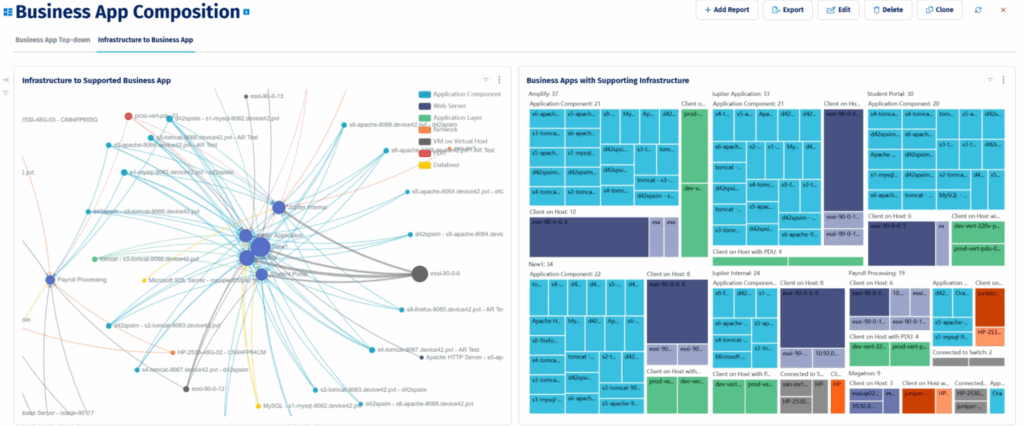
Asset dependency dashboard in Device42 (source)
Supply chain security
Another key activity in the NIS2 checklist is to ensure the security management of third parties. As reliance on vendor platforms and systems becomes the norm, some processes need to be in place to assess what potential threats and vulnerabilities are introduced with each new system acquisition or license subscription. This entails performing risk assessments for any new third-party vendors where company data will be processed in any way.
Here are some key considerations:
- Identifying the type of data that will be processed: Will there be any processing of confidential data, and if so, why? Will there be any cross-border transfer of personal data? Where will the data be stored?
- Assessing the vendor’s reliability: Has the vendor experienced a breach? Does it have any globally recognized security certifications? Can the company provide information on its security controls and best practices to understand how its system is protected? Are there any subcontractors to be assessed as well?
- Setting up appropriate contract terms and conditions: Can a tailored contract be set up, or is reliance on a standard agreement required? Can clauses be added regarding security responsibilities, confidentiality, vulnerability disclosure obligations, right to audit, etc.? Can incident response SLAs be negotiated?
- Monitoring critical vendors regularly: Did something change in the vendor’s security posture? Have there been any incidents? Is the vendor still processing the same type of data?
Any risks identified from the collected data need to be addressed to the appropriate decision-makers, and information about the newly introduced system needs to be reflected in the IT asset inventory and managed continuously.
Network and application security
Going deeper into technological controls, network and application security are among the NIS2 checklist requirements. There’s a multitude of solutions for securing cloud and physical networks, and plenty of developer tools to help with better code and automated testing. That said, all of these need to be orchestrated effectively, starting with the principles that dictate which security controls should be in place. Choosing the right tools is only one part of the process.
For networks, security controls include:
- Network segmentation and isolation
- Implementing logging and monitoring through Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
- Strong encryption for data in transit
- Data leakage protection mechanisms
- Review of network architecture rules
- Configuration management
- System and device authentication
- SSL certificate management
For applications, if we consider self-developed ones, a good software development lifecycle (SDLC) should be followed, including secure application requirements, four-eyes principles, secure coding practices such as data validation and sanitization, security training for developers for specific programming languages, segregation of environments, and security testing before rolling out any change.
Identity and access management
Unauthorized access is the most common way for threat actors to obtain critical information. Thus, the door to an organization’s environment is only as strong as its identity and access management (IAM) procedures and mechanisms. NIS2 doesn’t prescribe the controls to ensure a strong IAM, but your organization can leverage common best practices, such as these:
- Implementing role-based access control (RBAC): Access management becomes easier and safer by implementing an access control matrix based on roles rather than individuals. This can be achieved with the help of asset owners and line managers, who can indicate which baseline access requirements are needed. These individuals are able to take into account job responsibilities while avoiding toxic combinations, such as extended access to additional systems that would violate policy principles (least privilege or four-eyes).
- Recertifying access rights: As a necessary access control, recertification needs to be done periodically, with increased frequency on critical assets. To ensure completeness, active assets should be sourced from the central IT asset inventory. This is a detective control aimed at identifying and correcting deviations that occur following role changes and staff offboarding. However, continuous identity management, as a preventive control, is also essential to ensure the timely deactivation of access. Privileged access management needs increased attention in this process. Employee and contractor onboarding, offboarding, and internal movements can be automated with Freshworks Journeys, enabling a stronger, less error-prone access recertification process.
- Using strong authentication: Usernames and passwords are not sufficiently secure for accessing critical systems for your company and its customers. A multi-factor authentication (MFA) mechanism, such as SSO, should be implemented to mitigate the risk of ongoing password attacks.
Incident management
As attacks continue to evolve and intensify, with potentially systemic consequences, incident management is becoming a key topic related to NIS2 and most security regulations. Governments and in-scope organizations subject to the regulation are mandated to implement strong incident management processes.
Best practices indicate the following actions:
- Implement an incident management plan: Define how your company will respond to incidents. This includes processes for each stage of an incident, from its detection to its triage (assessment, classification), response (containment, mitigation), and lessons learned (or post-mortem). For each stage, the proper channels need to be activated, roles and responsibilities defined, and repeatable actions performed. Additionally, it’s a great idea to create incident playbooks for common scenarios, such as “ransomware,” “network downtime,” or “insider threat.” They should include step-by-step actions to take by incident responders to manage each particular incident type.
- Use early warning indicators: The earlier an incident is identified, the more effective the response can be. Integrate logging and monitoring capabilities, monitor your critical assets in real time, and educate your employees to report suspicious activity immediately. If possible, implement a security operations center (SOC) with first-line responders available outside regular business hours.
- Exercise the plan and train the incident responders: The incident management plan is only as good as the knowledge and coordination of the incident responders. These are the ones nominated to have roles and responsibilities in the plan, whether they are developers who can promptly patch a system, incident coordinators who keep stakeholders informed, or security operations that perform forensics. It may also involve third parties, like vendors, who are ideally bound by incident response SLAs defined in the contract with your organization. Regular training and scenario-based exercises are needed to familiarize people with their roles and identify weaknesses in the incident management plan.
Business continuity and crisis management
Going a step further, business continuity and crisis management are part of overall operational resilience. This means an organization needs to be ready to resume its critical business and operations in the adversity of unlikely but impactful scenarios that go beyond incident management. Such scenarios need to be assessed within a risk management process as well and may include core interruptions such as full platform downtime, critical vendor unavailability, or even people and building unavailability.
Recovery time objectives (RTOs) must be identified and implemented for processes and assets. This is done through a process called business impact analysis (BIA), in which the impact of the potential unavailability of processes and their dependencies, such as systems, is evaluated over a time scale. The purpose is to identify critical processes that, if interrupted, would pose a significant financial, client, or regulatory impact for the organization.
Business continuity and crisis management plans need to be created and tested on a regular basis to effectively respond to major disruptions. While no plan can address every potential scenario, these set a framework and expectations for actions to take and who to involve in decision-making and operational support. They also specify how to communicate internally and, especially, to external parties such as clients and regulators.
Training and awareness
Finally, organizations should not neglect employee and contractor training. All the governance and technological measures suggested above are incomplete without the human factor, which should become a security enabler, rather than a security weakness. Phishing, social engineering, connecting to a public rogue Wi-Fi, man-in-the-middle attacks, and other threats are not possible without human action.
Employees need to be educated on these threats to decrease their susceptibility to attacks and increase their anomaly-spotting skills.
Training and awareness are best done differently for various groups, conveying targeted information:
- All staff: Everyone should, at a minimum, receive information on phishing, acceptable use of assets, and the process for reporting incidents. Combine mandatory training with gamification to increase engagement.
- Sensitive roles: Depending on the role, training should consider the responsibilities of the audience. For instance, finance needs to be aware of C-level impersonations and how to avoid falling for deceitful requests for money transfer. Incident responders need scenario-based incident management drills. Developers benefit from education on secure coding practices.
- Management: Managers are often targets of whaling and spear phishing and usually less aware of company device security policies, so they benefit from in-person, tailored security training.
Takeaway
The NIS2 checklist runs through the minimum requirements outlined by the European directive. To implement a tailored security program, NIS2 is best used in conjunction with other frameworks, such as ISO 27001, SOC 2 criteria, and NIST standards, which go a step further in prescribing best practice security controls.
Furthermore, the design and implementation of security requirements, whether they stem from NIS2 or other regulations, is not a one-time effort. Risks need to be identified and treated as part of regular BIAs audits, supply chain due diligence, testing, and learning lessons from incidents. Simultaneously, compliant and competitive organizations must apply continuous monitoring of their security posture, including asset management, change management, and ongoing training.
Sign up for a demo to see how Device42 can help with the foundational asset inventory and continuous discovery.