Software Audit & Compliance
USE CASE
Challenge
IT Infrastructure teams are typically required to conduct, assist in, and endure a number of different types of audit every year – finance audits, security audits, risk-related audits, budget cycle audits, and more.
A software audit can be particularly difficult if:
- You don’t have an accurate inventory of all your software
- The data you do have exists only in somebody’s head, or you have personnel changes
- Software is frequently installed and removed on servers and end-user machines without a record
A common strategy is to attempt a “full inventory” in order to prepare for a software audit with results stored in Excel and/or Visio files.
This approach is problematic for several reasons:
It can take weeks or months to get everything documented and organized into Excel.
By the time the software inventory is completed, so many things have been changed that it’s again out of date. At best, it will be out of date come the next audit.
Even if you create processes to keep your spreadsheet up-to-date, you will inevitably end up with multiple versions, resulting in data issues as there is no centralized editing support and no standardized data template.
While it might be possible to keep some data up to date manually, other data such as IP usage is virtually impossible to track manually.
Solution
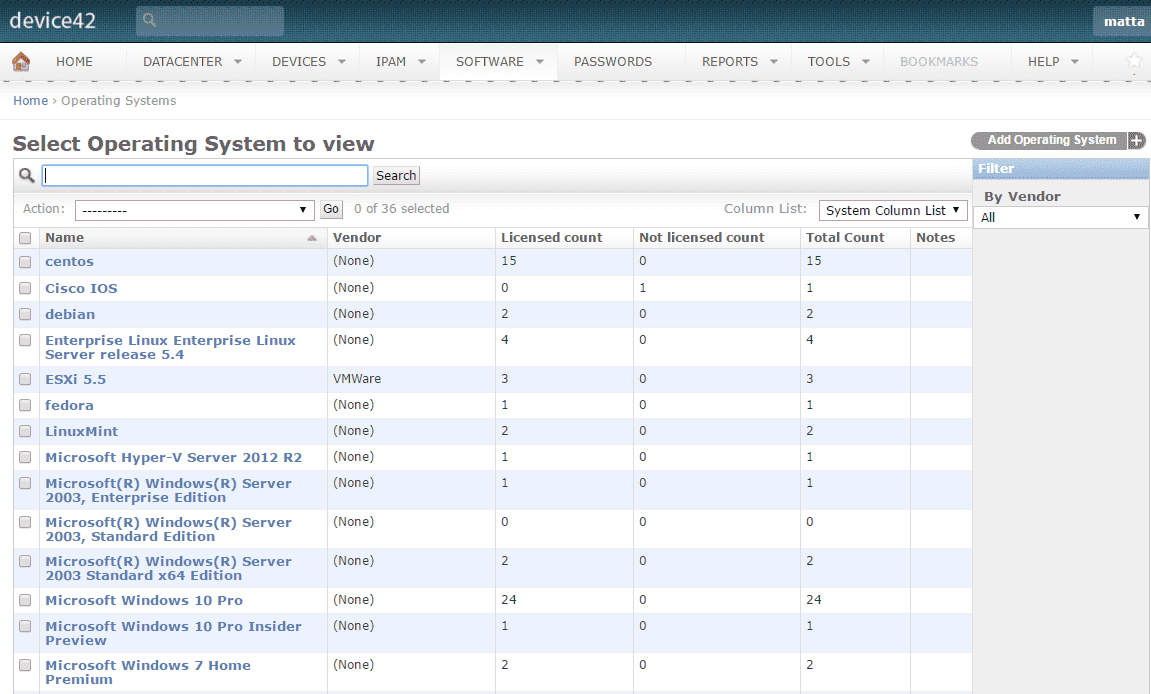
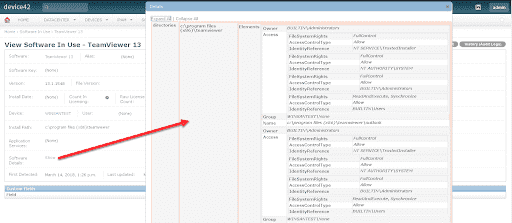
Using Device42’s powerful agentless software discovery process, organizations can create and maintain a comprehensive, accurate profile of all deployed software on Windows, Linux, and BSD machines alike across the entire IT infrastructure — from the server to the desktop level.
Highlights
Compare current usage to license counts
Detect prohibited software and generate immediate alerts
Track license agreements and expiration dates
Identify purchased vs. installed software
Supports common licensing models (user, device, CPU, key)
Provide customizable notification alerts for licensing issues
Auto-Discovers
Discovery can be run on a schedule so you can stop playing catch-up.
Auditing is no longer a giant undertaking to identify a ‘point in time’ state of your infrastructure.
Less manual entry, reduced investment of time & manpower, and fewer errors.
Compliance
License compliance– identify over-licensed, unlicensed, and expired licenses.
Standards assurance– identify prohibited and approved software.
Cost management– report license costs and minimize under-licensed software.
Utilizes Existing Data
Data in spreadsheets and CSV files can be ingested and organized, eliminating duplicated effort.
Data can be pulled from external systems such as Microsoft SCCM and BMC Remedy.
Flexible
Select software as ignored – removes software components from the discovery list and ignores these components in future discoveries.
Mark software as prohibited – sends alerts whenever prohibited software is located on the network.
Assign software to a suite – defines software as part of a software grouping, or “suite”.
Run IT with confidence.®